Phishing Analysis 2
Overview
- Platform: BTLO
- Category: Email / Phishing
- Tools: Thunderbird (viewer), Text Editor, URL2PNG, CyberChef
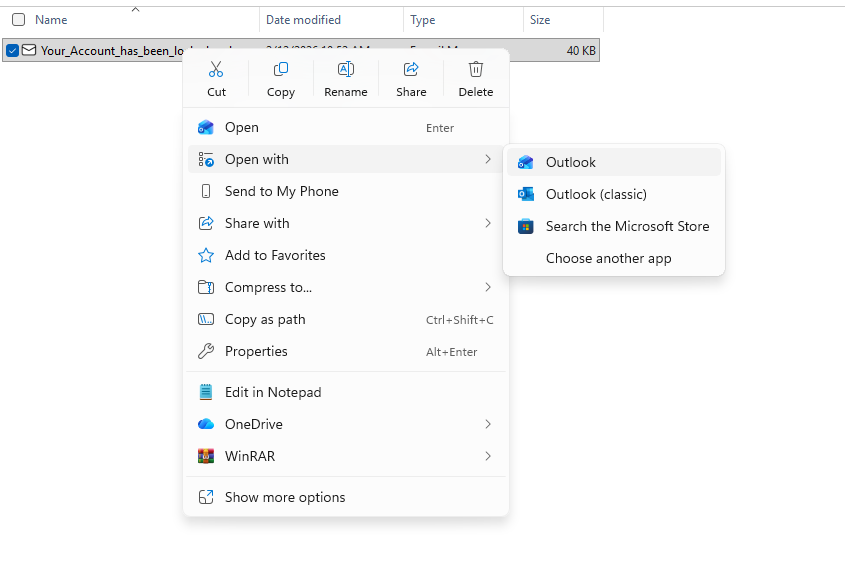
- Artifact:
Your_Account_has_been_locked.eml
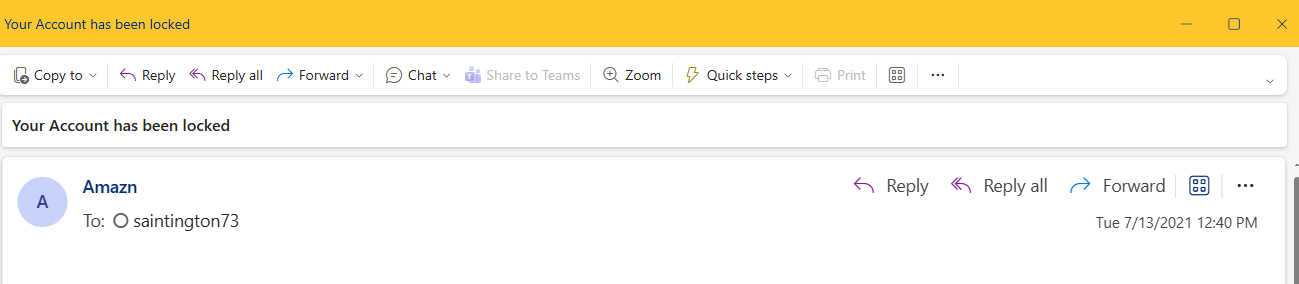
Q1. What is the sending email address?
Answer:
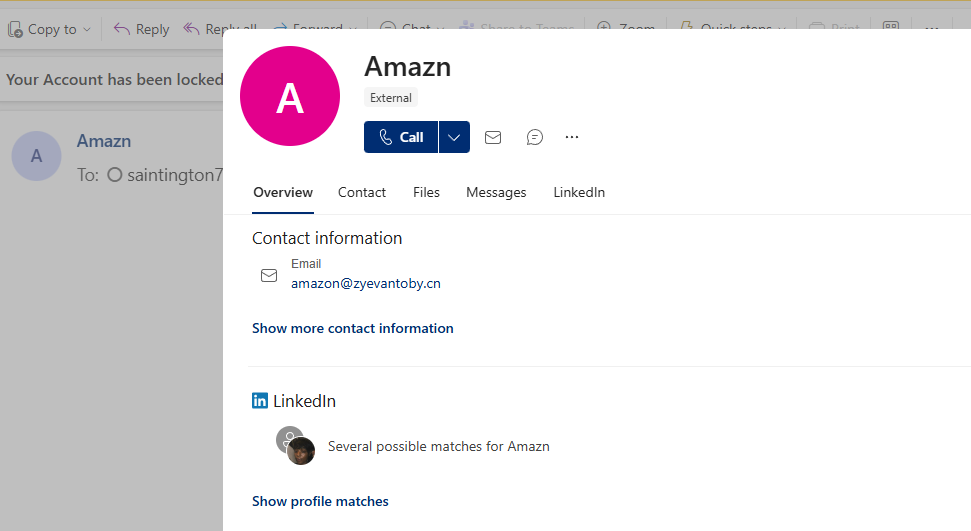
[email protected]
Process:
Opened the .eml in a mail client to view the sender details, then confirmed it in the raw headers.
Opened the .eml in a mail client and clicked the sender badge to expand the full address.
The visible name suggested “Amazon,” but the actual domain was zyevantoby.cn, which is a clear mismatch.
Q2. What is the recipient email address?
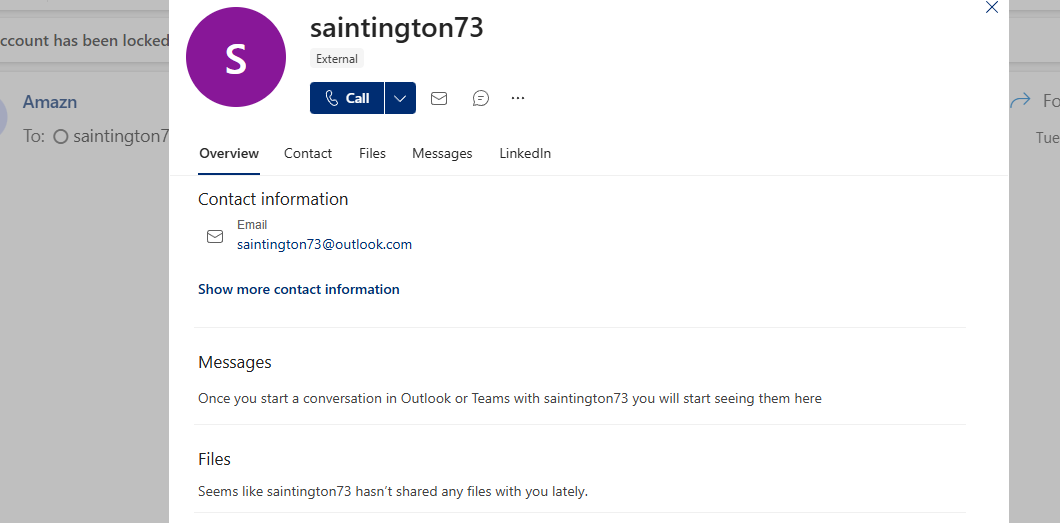
Answer:
[email protected]
Process:
Clicked the To: field in the message viewer and copied the full recipient address.
Q3. What is the subject line of the email?
Answer:
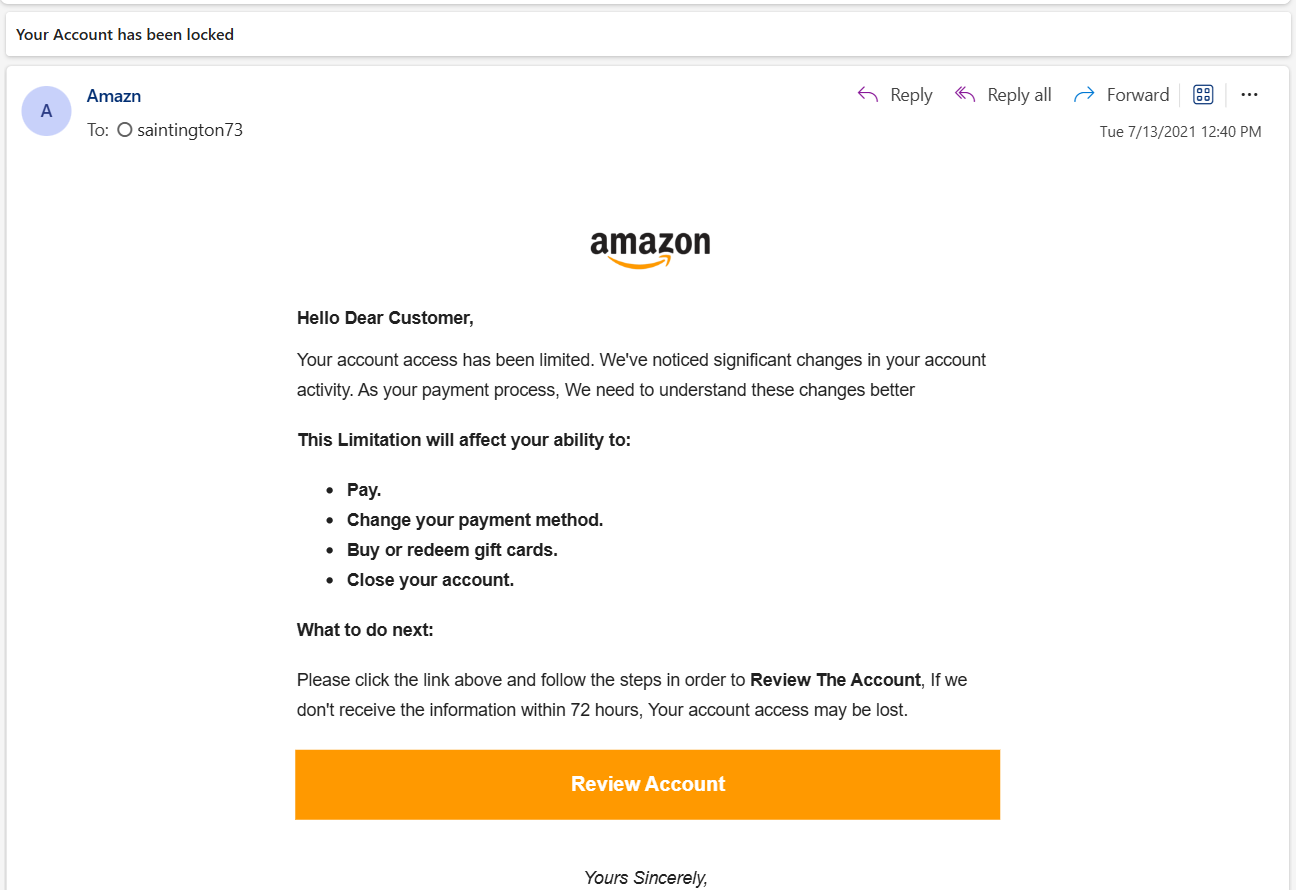
Your Account has been locked
Process:
Read the subject line directly in the email preview/header area.
Q4. What company is the attacker trying to imitate?
Answer:
Amazon
Process:
The brand name and logo in the body, plus the “Amazon” display name, indicate the attacker is imitating Amazon.
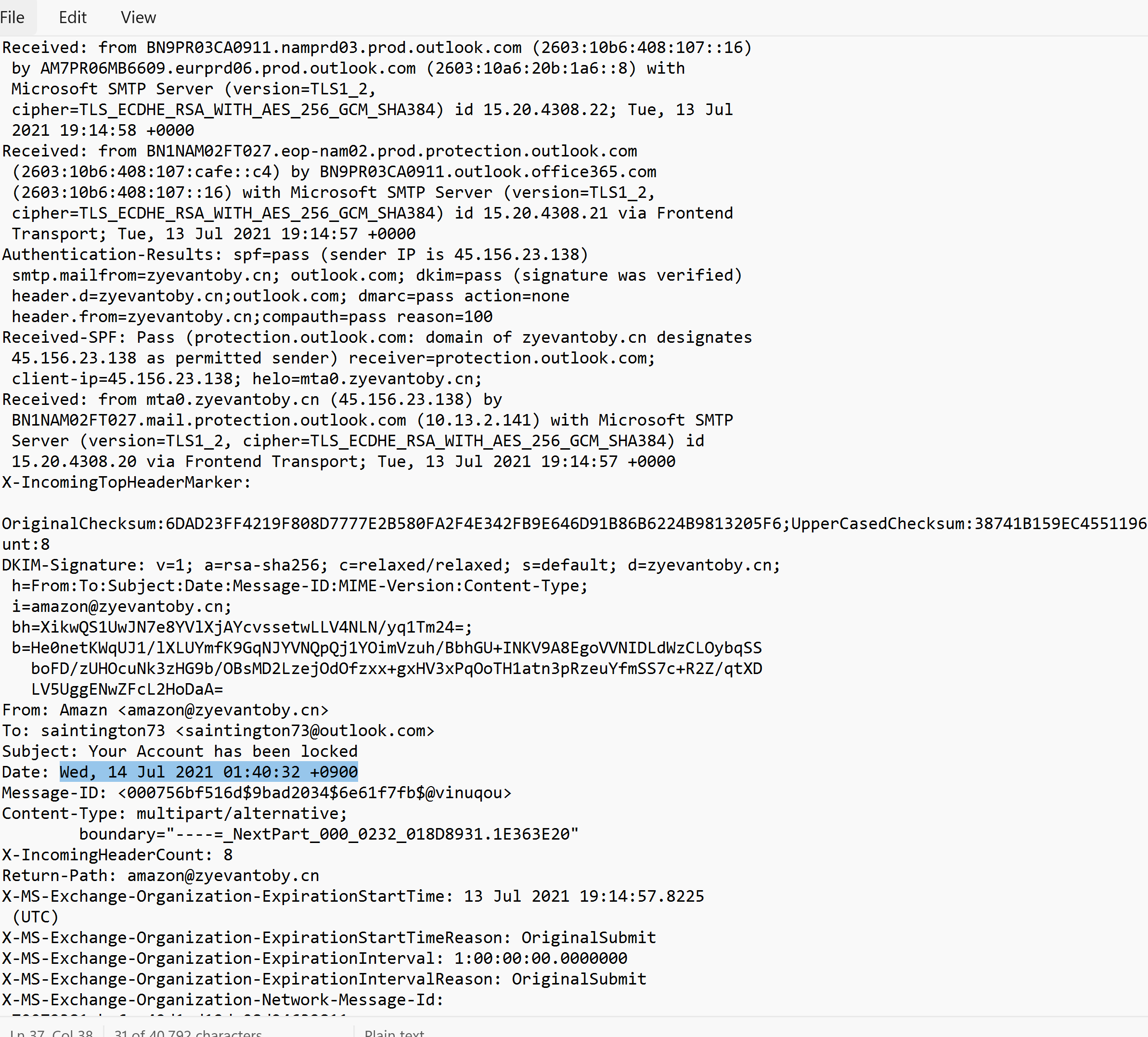
Q5. What is the date and time the email was sent?
Answer:
Wed, 14 Jul 2021 01:40:32 +0900
Process:
Opened the .eml in a text editor and copied the exact Date: header value (kept format intact).
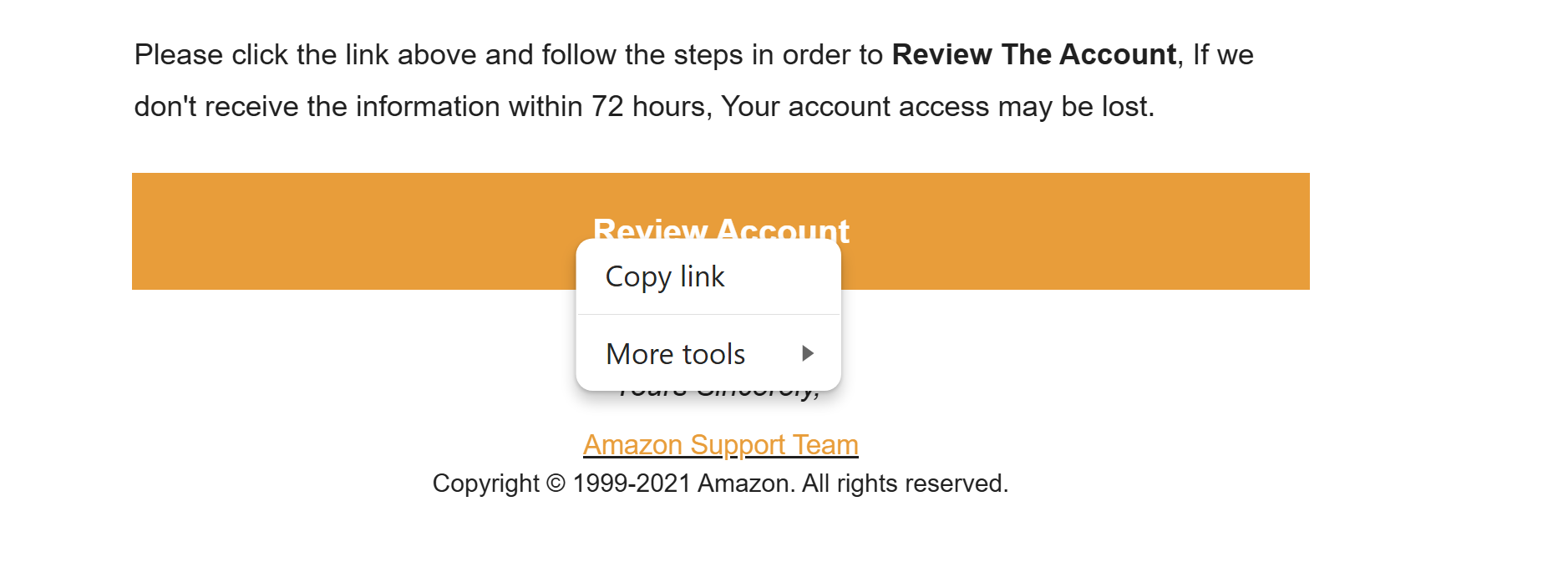
Q6. What is the URL of the main call-to-action button?
Answer:
https://emea01.safelinks.protection.outlook.com/?url=https%3A%2F%2Famaozn.zzyuchengzhika.cn%2F%3Fmailtoken%3Dsaintington73%40outlook.com&data=04%7C01%7C%7C70072381ba6e49d1d12d08d94632811e%7C84df9e7fe9f640afb435aaaaaaaaaaaa%7C1%7C0%7C637618004988892053%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C1000&sdata=oPvTW08ASiViZTLfMECsvwDvguT6ODYKPQZNK3203m0%3D&reserved=0
Process:
Copied the CTA link from the HTML anchor behind the “Review Account” button.
This URL is wrapped by Microsoft Safe Links, which hides the real destination in a query parameter.
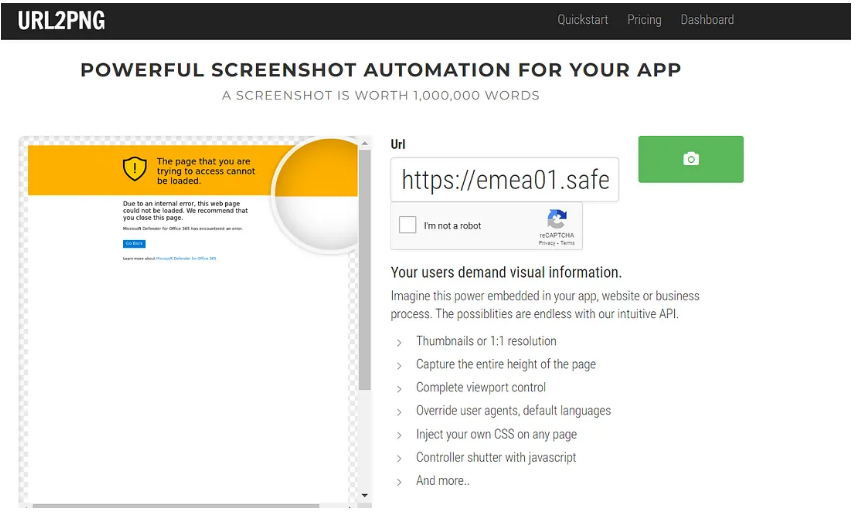
Q7. URL2PNG heading text
Answer:
This web page could not be loaded.
Process:
Pasted the CTA URL into URL2PNG and recorded the first heading shown on the rendered page.
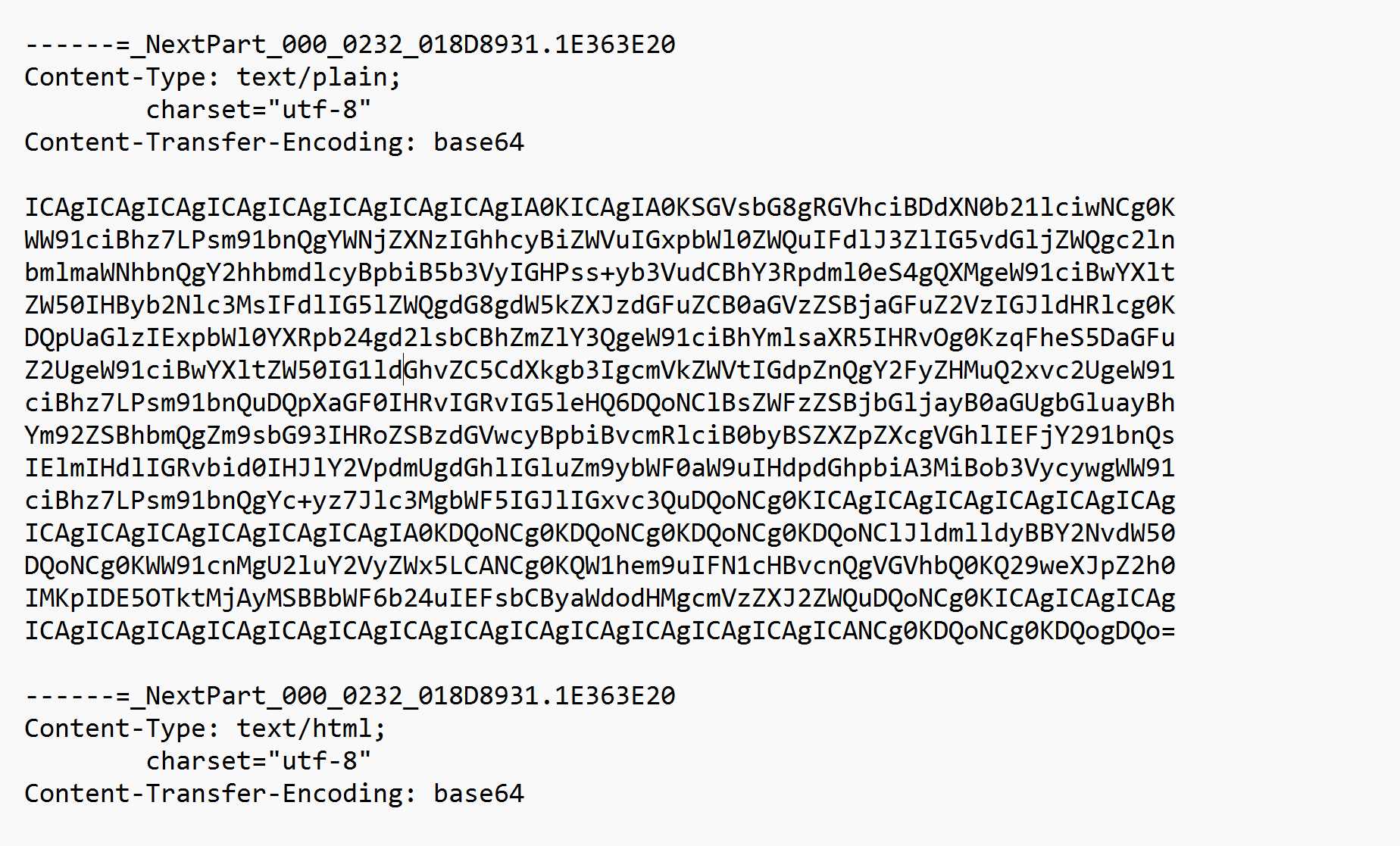
Q8. What encoding scheme is being used?
Answer:
base64
Process:
Located Content-Transfer-Encoding: base64 in the raw email headers/body.
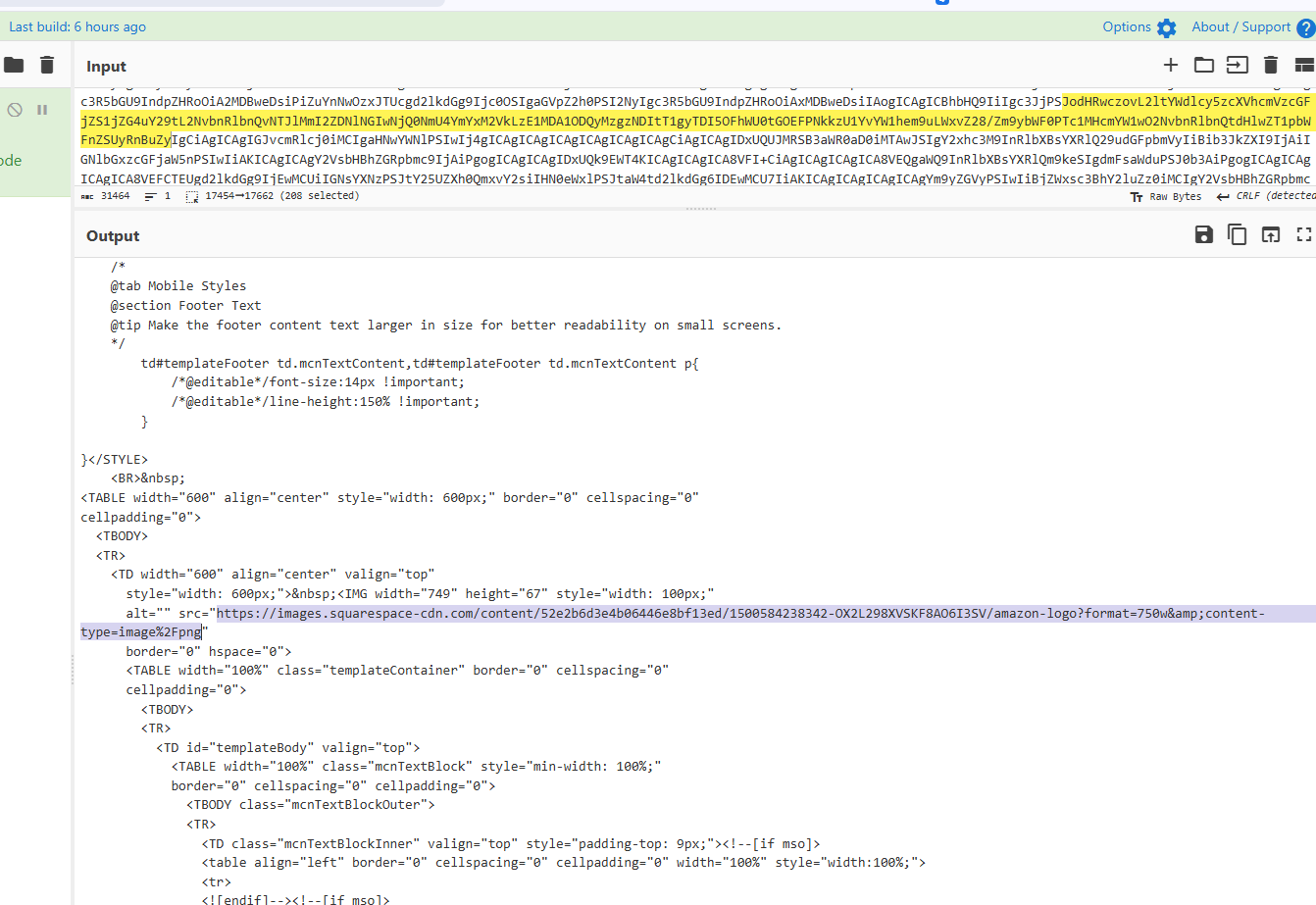
Q9. What is the URL used to retrieve the company’s logo?
Answer:
https://images.squarespace-cdn.com/content/52e2b6d3e4b06446e8bf13ed/1500584238342-OX2L298XVSKF8AO6I3SV/amazon-logo?format=750w&content-type=image%2Fpng
Process:
The HTML body is base64 encoded. I decoded it in CyberChef and extracted the image source URL from the HTML.
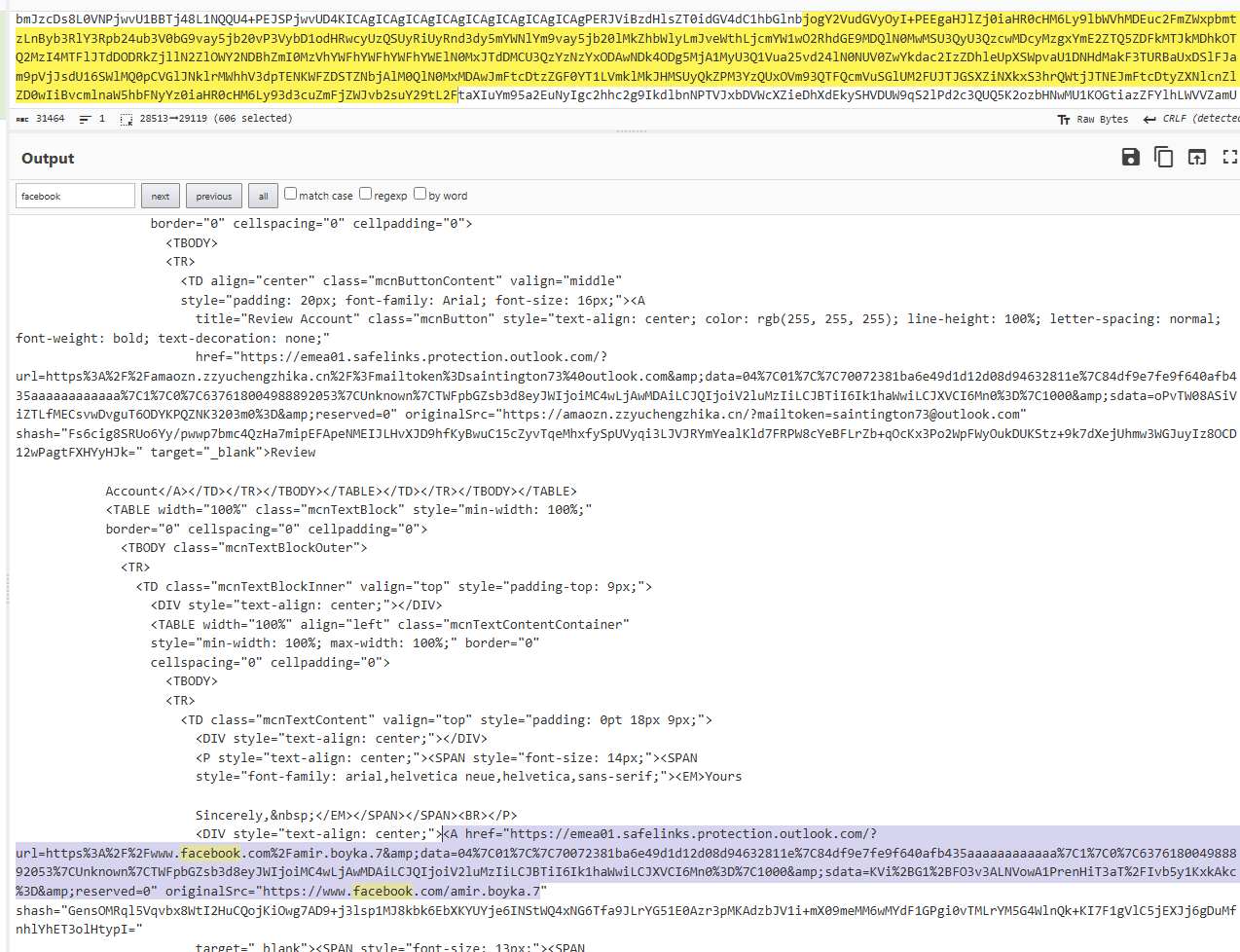
Q10. Facebook username found in URL
Answer:
amir.boyka.7
Process:
Searched the decoded HTML for “facebook”. The URL contains a profile link with username amir.boyka.7.
Final Answers (for submission)
- [email protected]
- [email protected]
- Your Account has been locked
- Amazon
- Wed, 14 Jul 2021 01:40:32 +0900
- https://emea01.safelinks.protection.outlook.com/?url=https%3A%2F%2Famaozn.zzyuchengzhika.cn%2F%3Fmailtoken%3Dsaintington73%40outlook.com&data=04%7C01%7C%7C70072381ba6e49d1d12d08d94632811e%7C84df9e7fe9f640afb435aaaaaaaaaaaa%7C1%7C0%7C637618004988892053%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C1000&sdata=oPvTW08ASiViZTLfMECsvwDvguT6ODYKPQZNK3203m0%3D&reserved=0
- This web page could not be loaded.
- base64
- https://images.squarespace-cdn.com/content/52e2b6d3e4b06446e8bf13ed/1500584238342-OX2L298XVSKF8AO6I3SV/amazon-logo?format=750w&content-type=image%2Fpng
- amir.boyka.7