Operation Blackout 2025
Scenario
Byte Doctor suspected process injection activity on a Windows endpoint. The objective was to verify the injection technique and identify the exact API sequence used to inject into a legitimate process.
Provided files:
Ghost-Thread.apmx64(API Monitor capture)inject.exe.i64(IDA database)INSTRUCTIONS.txt
Artifact Selection and Relevance
inject.exe.i64:- Static view of malware logic and function flow.
- Used to identify TLS callback behavior and injection functions before runtime validation.
Ghost-Thread.apmx64:- Runtime API trace of actual behavior on execution.
- Used to confirm target process, process handle usage, memory allocation, and thread creation.
INSTRUCTIONS.txt:- Provides analysis workflow and expected tool context (
API Monitor,IDA).
- Provides analysis workflow and expected tool context (
Investigation
Step 1: Validate provided evidence set
C:\Users\dfirrocks\Desktop\GhostThread>dir
Volume in drive C has no label.
Volume Serial Number is 860A-2B89
Directory of C:\Users\dfirrocks\Desktop\GhostThread
03/01/2026 10:57 AM <DIR> .
03/01/2026 08:59 AM <DIR> ..
04/16/2025 11:11 PM 3,566,037 Ghost-Thread.apmx64
04/16/2025 09:59 PM 2,328,822 inject.exe.i64
04/16/2025 11:22 PM 934 INSTRUCTIONS.txt
3 File(s) 5,895,793 bytes
2 Dir(s) 38,238,740,480 bytes free
C:\Users\dfirrocks\Desktop\GhostThread>type INSTRUCTIONS.txt
==> Open the 'inject.exe.i64' file using IDA Freeware.
==> Instructions for API Monitor
...
Purpose: verify artifact scope and tool chain before deep analysis.
Logic: baseline triage reduces misalignment between static and dynamic evidence.
What this proves: all required artifacts are present and aligned to the scenario.
Next: identify the injection style from static logic.
Step 2: Identify injection style (TLS callback)
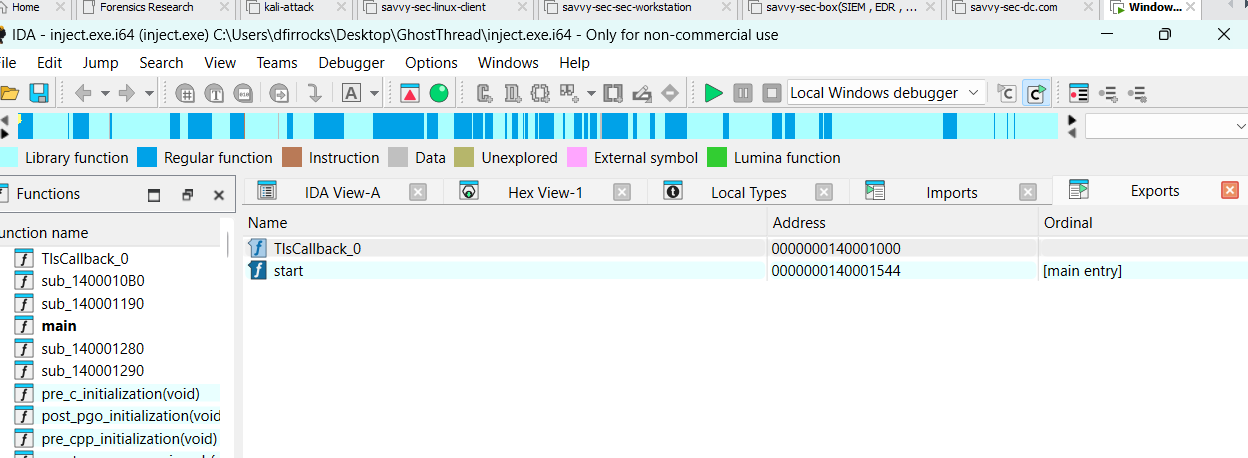
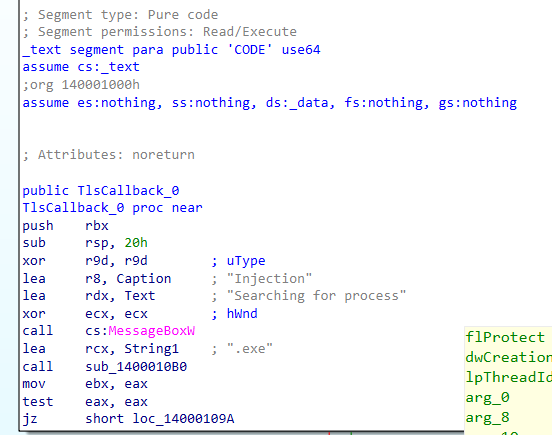
In IDA export/function view, TlsCallback_0 appears before normal entry flow and triggers malicious logic before main().
Purpose: classify the attacker execution method.
Logic: TLS callbacks execute during loader initialization, before normal program entry.
What this proves: injection chain is initiated through a Thread Local Storage (TLS) callback mechanism.
Next: trace how the sample enumerates processes.
Step 3: Confirm process enumeration API
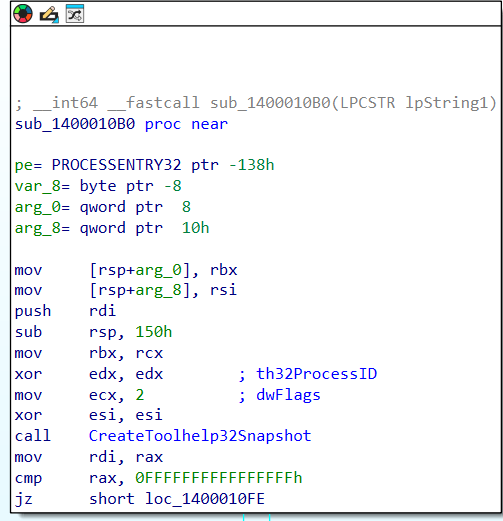
Post-MessageBoxW, execution pivots to an internal function (sub_140001190) that performs process discovery.
The function issues:
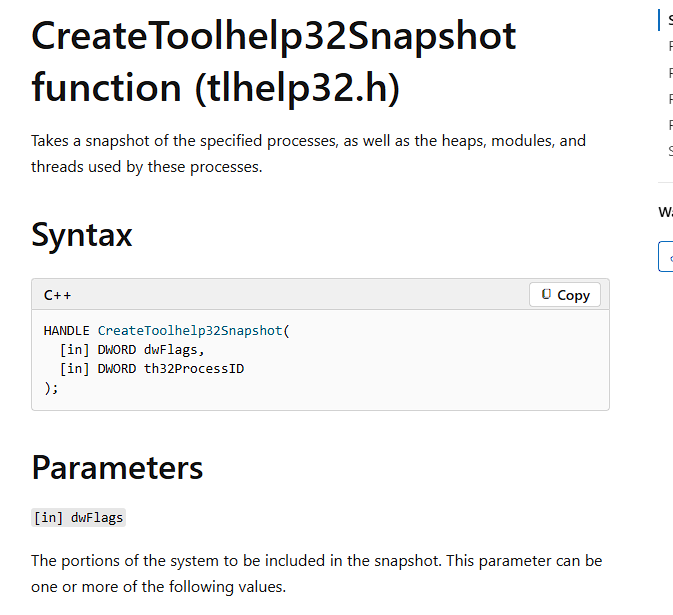
CreateToolhelp32Snapshot(TH32CS_SNAPPROCESS, 0)Process32First- Loop with
Process32Next - Name comparison using
lstrcmpA
Purpose: determine how the malware locates an injection target.
Logic: snapshot + iterative process traversal is a standard target-selection pattern.
What this proves: API used to list processes is CreateToolhelp32Snapshot.
Next: identify the specific process being hunted.
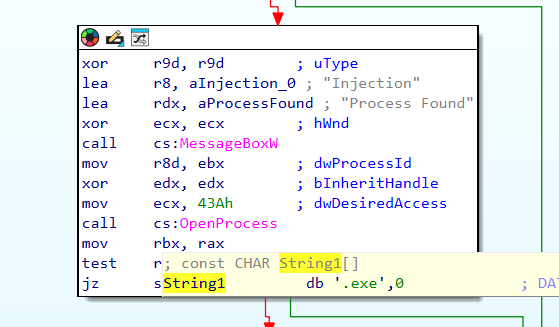
Step 4: Determine targeted process
Comparison logic loops until process name match; API Monitor/IDA context shows lookup for notepad.exe.
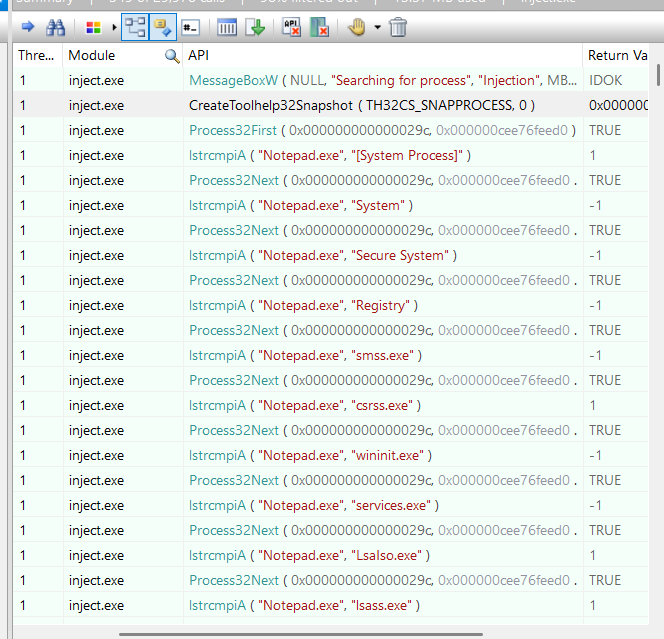
Purpose: identify victim process for remote injection.
Logic: repeated name comparison followed by OpenProcess indicates explicit target selection.
What this proves: target process is notepad.exe.
Next: capture the concrete PID from runtime telemetry.
Step 5: Capture target PID from OpenProcess
API trace records the process handle open against the matched process.
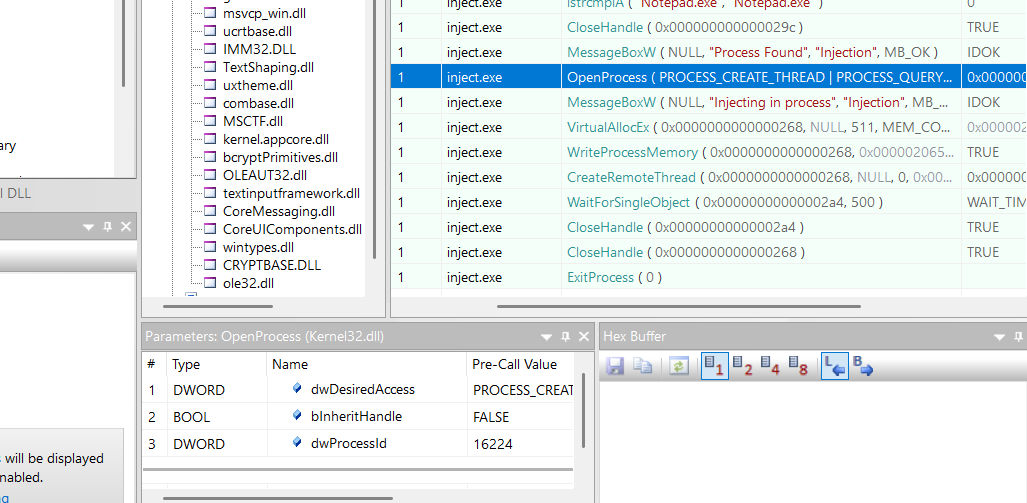
Purpose: map logical target to concrete process instance.
Logic:OpenProcessbinds the injector to a specific PID.
What this proves: target PID is 16224.
Next: quantify payload allocation size.
Step 6: Extract shellcode size from allocation call
In the injection function path, memory is allocated in the remote process and the allocation size (nSize) is visible.
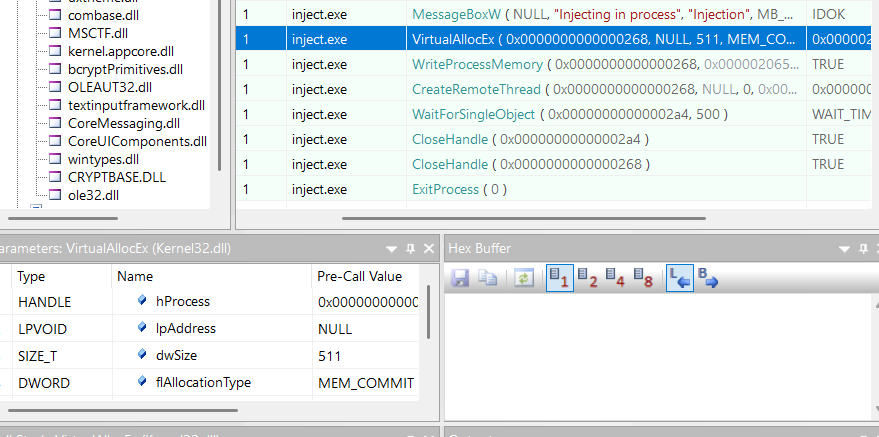
Purpose: identify exact payload size used in remote memory stage.
Logic:VirtualAllocEx/allocation parameter reflects intended shellcode length.
What this proves: shellcode size is 511 bytes.
Next: verify execution transfer into remote process.
Step 7: Confirm payload execution API
After memory allocation and write stage, execution is triggered in the remote process.
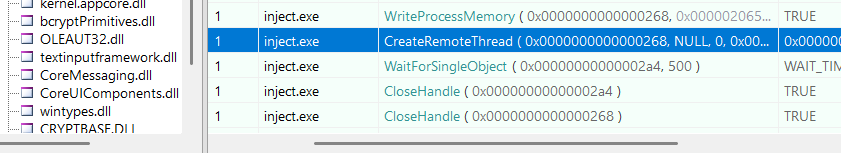
Purpose: validate final execution step of process injection chain.
Logic: remote thread creation is the execution primitive afterWriteProcessMemory.
What this proves: injected payload is started via CreateRemoteThread.
Next: verify why sample terminates before normal entry.
Step 8: Confirm pre-main termination behavior
The trace shows explicit process termination before legitimate program flow.
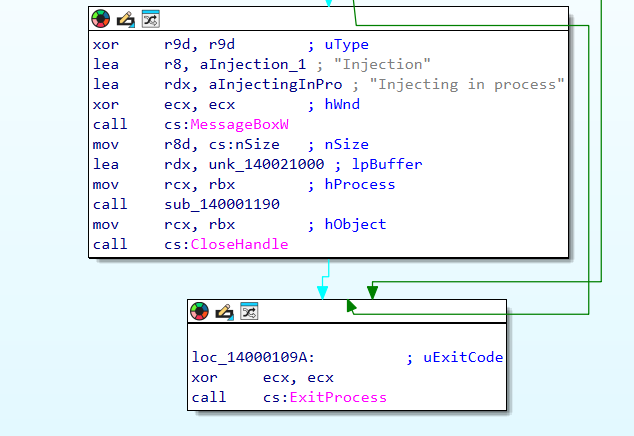
Purpose: explain control-flow behavior tied to TLS execution.
Logic: TLS callback executes early, thenExitProcessends binary before normal app logic.
What this proves: API responsible for termination beforemain()is ExitProcess.
Timeline
2025-04-16Capture artifacts generated (.apmx64,.i64) for analysis set.T0TLS callback executes prior to normal entry point.T1Process enumeration begins withCreateToolhelp32Snapshot+Process32First/Next.T2Target processnotepad.exeidentified and opened (PID 16224).T3Remote memory allocated (511bytes), payload written.T4Remote execution triggered withCreateRemoteThread.T5Sample exits viaExitProcessbefore reaching normalmain()flow.
Final Answers (for submission)
Thread Local StorageCreateToolhelp32Snapshotnotepad.exe16224511CreateRemoteThreadExitProcess
Tool Significance
IDA Free:- Static reverse engineering for functions, imports, callback logic, and call graph pivots.
API Monitor:- Dynamic API telemetry to validate execution chain and arguments (enumeration, open process, memory ops, remote thread).
- Why both matter:
IDAexplains intent and execution flow.API Monitorproves runtime behavior and confirms the answers with observable API calls.