Campfire-1
Scenario
Alonzo spotted suspicious files on his system. SOC suspected a Kerberoasting attack and provided three artifact sets:
- Security logs from Domain Controller (
SECURITY-DC.evtx) - PowerShell-Operational logs from workstation
- Prefetch files from workstation
Artifact Selection and Relevance
SECURITY-DC.evtx: definitive source for Kerberos service ticket requests (4769) and client IP attribution.Powershell-Operational.evtx: execution telemetry for script block logging (4104) to identify recon and staging activity.RUBEUS.EXE-*.pf: endpoint execution proof with executable path and last-run timestamp.
Investigation
Step 1: Baseline detections with Sigma (Chainsaw hunt)
chainsaw hunt *.evtx \
--sigma /opt/chainsaw/sigma/ \
--sigma /opt/chainsaw/hayabusa-rules/sigma/ \
--mapping /opt/chainsaw/mappings/sigma-event-logs-all.yml
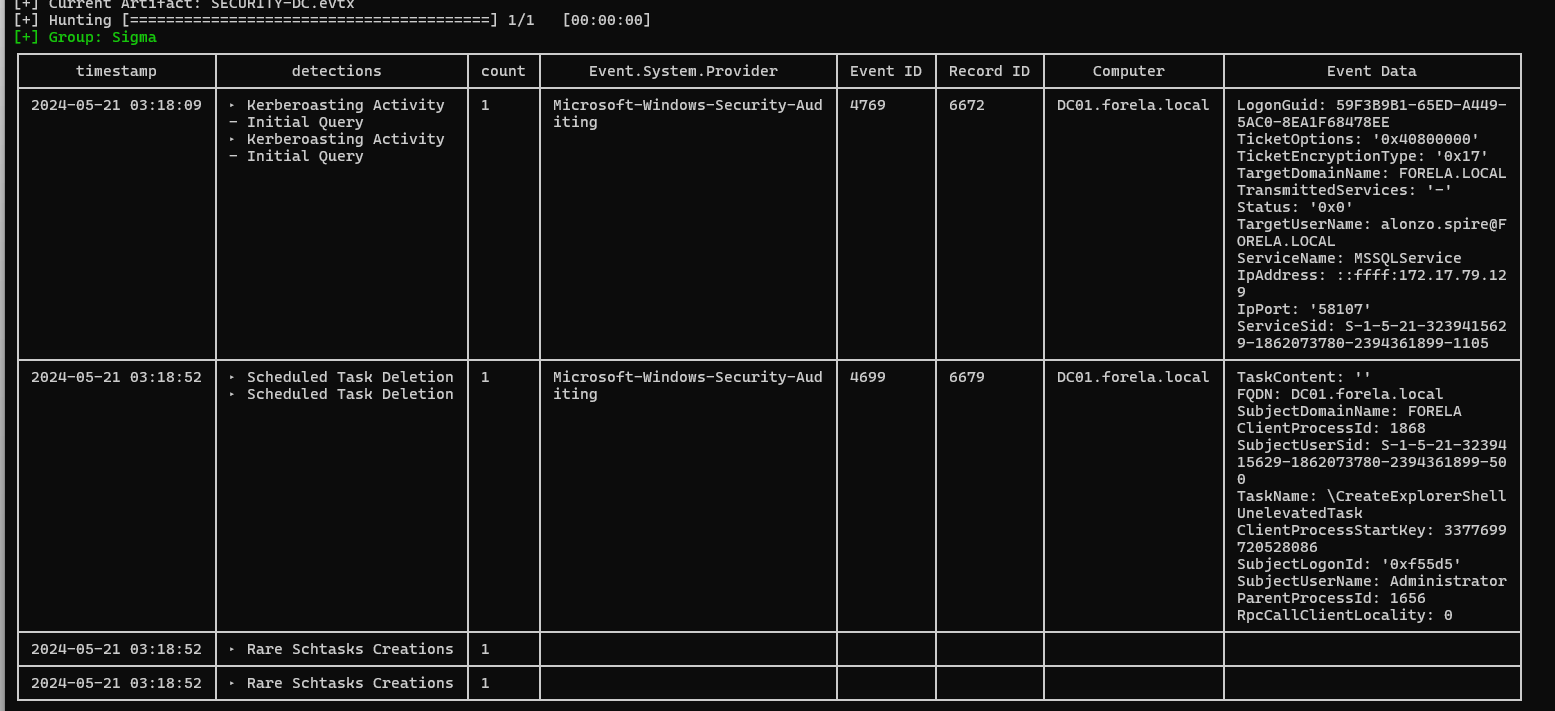
Purpose: Quickly surface suspicious detections across provided logs.
Logic: Run broad Sigma coverage before deep manual filtering.
What this proves: Kerberoasting-related activity appears and points toward Event ID4769+ workstation telemetry.
Next: dump DC security log to JSON for precise parsing.
Step 2: Dump DC events to JSON
chainsaw dump SECURITY-DC.evtx --json > events.json
Purpose: Convert EVTX into a queryable format.
Logic: JSON allows deterministic filtering withjq.
What this proves: We can pivot by event IDs, service names, users, and timestamps.
Next: profile the event ID distribution.
Step 3: Enumerate event IDs in DC log
jq -r '.[].Event.System.EventID' events.json | sort -n | uniq -c > events.txt
cat events.txt
12 4662
11 4688
1 4696
1 4698
1 4699
19 4702
7 4768
16 4769
177 4771
20 4799
1 4826
8 5140
6 5142
13 5379
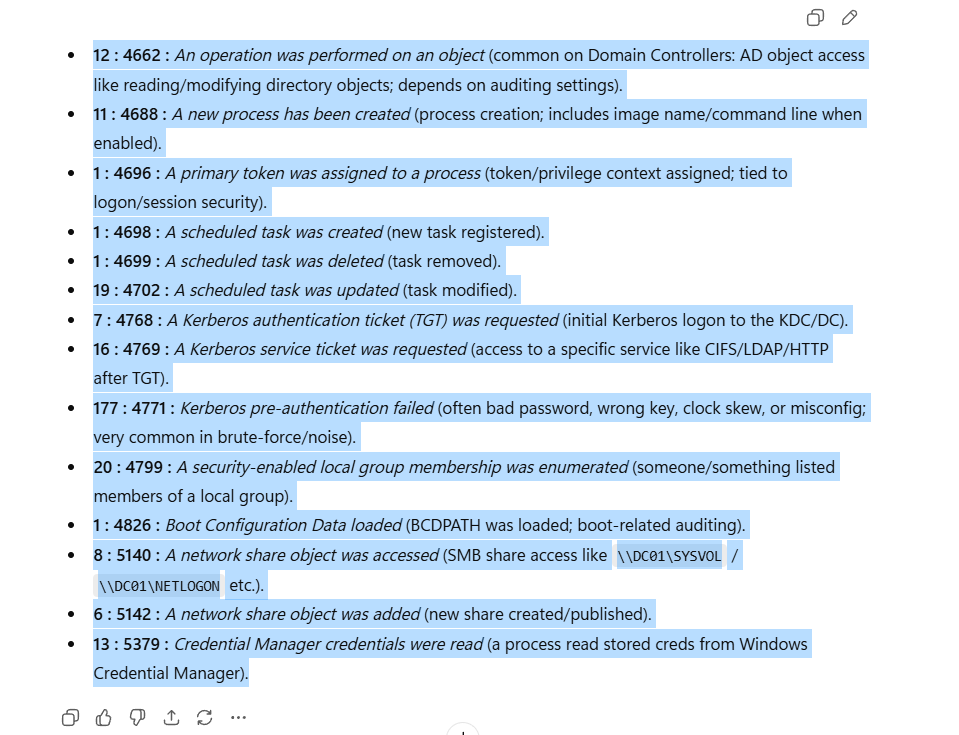
Purpose: Identify Kerberos-relevant event families.
Logic: Prioritize4769for service ticket requests linked to Kerberoasting.
What this proves: There are enough4769events to isolate malicious TGS requests.
Next: profile user/service combinations in4769.
Step 4: Identify suspicious 4769 user/service combos
jq -r '.[] | select(.Event.System.EventID==4769) | .Event.EventData.TargetUserName' events.json | sort | uniq -c | sort -nr
jq -r '
.[]
| select(.Event.System.EventID==4769)
| [.Event.EventData.TargetUserName,.Event.EventData.ServiceName,.Event.EventData.ServiceSid]
| @tsv
' events.json | sort | uniq -c | sort -nr
10 [email protected] DC01$ S-1-5-21-...-1000
2 [email protected] DC01$ S-1-5-21-...-1000
1 [email protected] krbtgt S-1-5-21-...-502
1 [email protected] MSSQLService S-1-5-21-...-1105
1 [email protected] FORELA-WKSTN001$ S-1-5-21-...-1106
1 [email protected] DC01$ S-1-5-21-...-1000
Purpose: find user-to-service anomalies in TGS requests.
Logic: rare request to a roastable SPN (MSSQLService) from user context is suspicious.
What this proves:alonzo.spirerequested a ticket forMSSQLService.
Next: extract the exact event to answer time/service/IP questions.
Step 5: Extract the kerberoasting event
jq -r '
.[]
| select(.Event.System.EventID==4769)
| select(.Event.EventData.ServiceName=="MSSQLService")
' events.json
Key fields from event:
SystemTime: 2024-05-21T03:18:09.459682Z
TargetUserName: [email protected]
ServiceName: MSSQLService
TicketEncryptionType: 0x17
IpAddress: ::ffff:172.17.79.129
Purpose: confirm direct evidence of Kerberoasting request.
Logic: isolate4769whereServiceName == MSSQLServiceand inspect encryption/IP/user tuple.
What this proves: kerberoasting activity occurred at2024-05-21 03:18:09 UTC, targetingMSSQLService, from172.17.79.129.
Next: validate endpoint-side execution path using PowerShell logs.
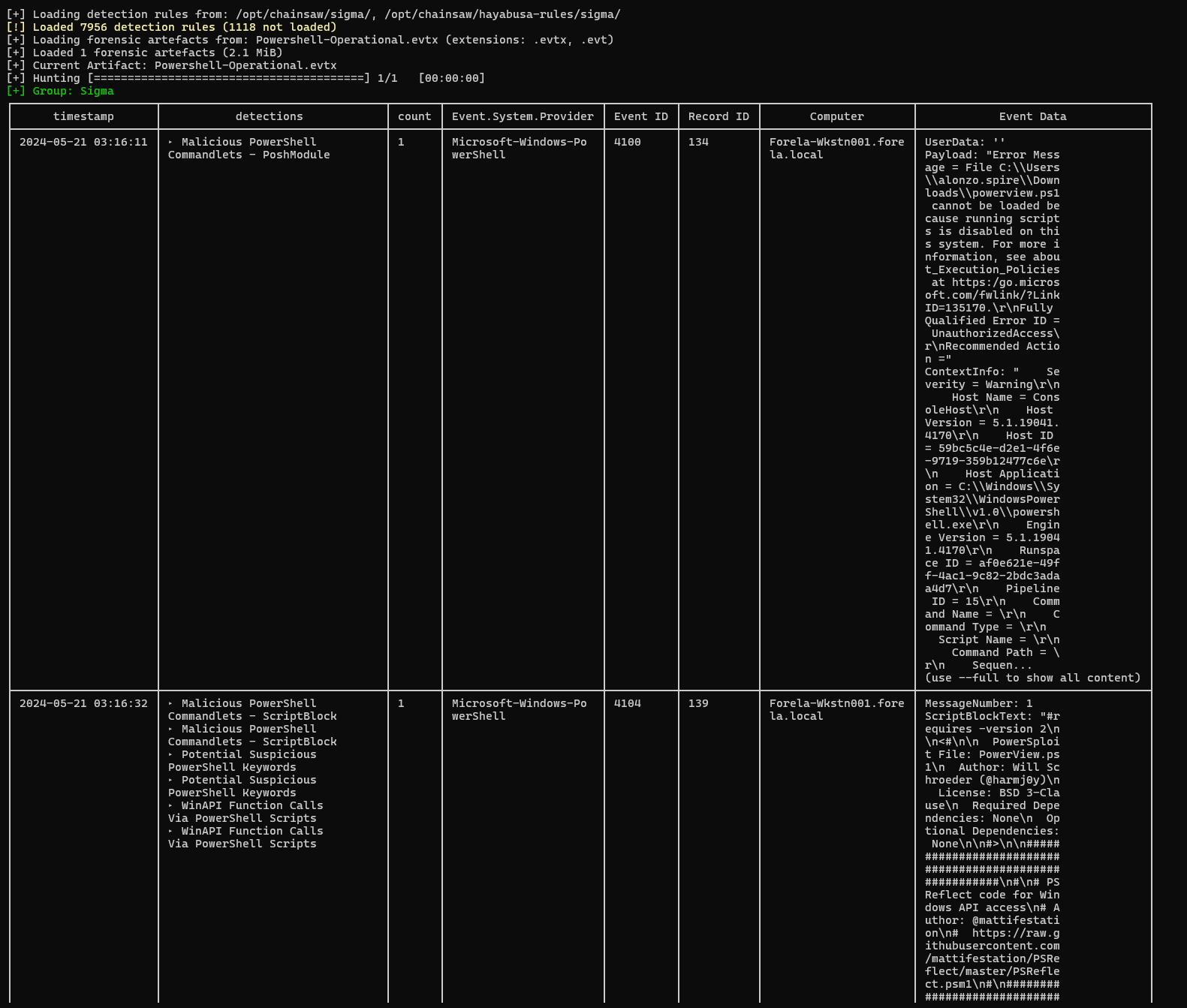
Step 6: Profile PowerShell operational events
jq -r '.[].Event.System.EventID' powershellop.json | sort -n | uniq -c
1 4100
29 4104
4 40961
4 40962
4 53504
jq -c '.[] | select(.Event.System.EventID==4104)' powershellop.json | head -2 | tail -1 | jq '.Event.EventData'
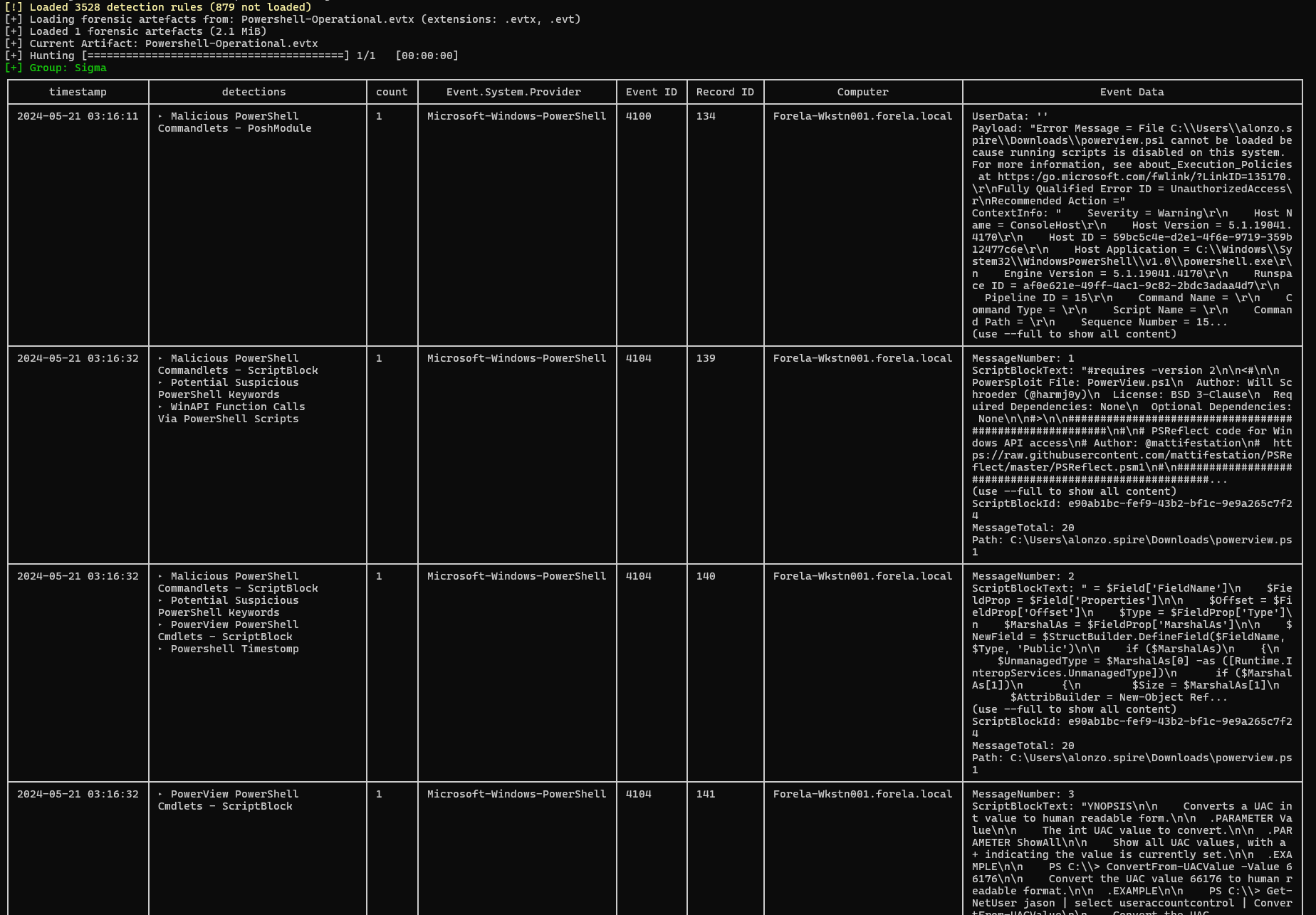
Purpose: identify script block activity related to AD reconnaissance/roasting prep.
Logic:4104contains full or partial script text and file path metadata.
What this proves: PowerView execution appears in script block logs.
Next: extract file path and execution time forpowerview.ps1.
Step 7: Confirm powerview.ps1 execution and UTC time
jq -c '.[] | select(.Event.System.EventID==4104) | .Event.EventData.Path' powershellop.json | uniq -c
1 ""
28 "C:\Users\alonzo.spire\Downloads\powerview.ps1"
jq -c '
.[]
| select(.Event.System.EventID==4104)
| select(.Event.EventData.Path=="C:\\Users\\alonzo.spire\\Downloads\\powerview.ps1")
' powershellop.json | head -1 | jq .Event.System.TimeCreated_attributes.SystemTime
"2024-05-21T03:16:32.588340Z"
Purpose: determine the recon script name and launch time.
Logic: filter by4104then constrain by script path.
What this proves:powerview.ps1executed at2024-05-21 03:16:32 UTC.
Next: validate kerberoasting tool execution from prefetch.
Step 8: Locate and parse Rubeus prefetch artifact
ls C/Windows/prefetch/ | wc -l
ls C/Windows/prefetch/ | grep RUBEUS
212
RUBEUS.EXE-5873E24B.pf
PECmd.exe -f ..\campfire-1\Triage\Workstation\2024-05-21T033012_triage_asset\C\Windows\prefetch\RUBEUS.EXE-5873E24B.pf
Key extracted fields:
Executable name: RUBEUS.EXE
Run count: 1
Last run: 2024-05-21 03:18:08
Referenced file: \USERS\ALONZO.SPIRE\DOWNLOADS\RUBEUS.EXE
PECmd.exe -f ..\campfire-1\Triage\Workstation\2024-05-21T033012_triage_asset\C\Windows\prefetch\RUBEUS.EXE-5873E24B.pf
Executable name: RUBEUS.EXE
Run count: 1
Last run: 2024-05-21 03:18:08
Referenced file: \USERS\ALONZO.SPIRE\DOWNLOADS\RUBEUS.EXE
Purpose: prove endpoint execution of roasting tool and collect full path/time.
Logic: prefetch tracks executable path and run timestamps independent of event logs.
What this proves:Rubeus.exeexecuted fromC:\Users\Alonzo.spire\Downloads\Rubeus.exeat2024-05-21 03:18:08 UTC.
Next: align answers with challenge prompts.
Step 9: Full command log (raw workflow)
All commands you ran are preserved below in condensed order.
chainsaw hunt *.evtx --sigma /opt/chainsaw/sigma/ --sigma /opt/chainsaw/hayabusa-rules/sigma/ --mapping /opt/chainsaw/mappings/sigma-event-logs-all.yml
chainsaw dump SECURITY-DC.evtx --json > events.json
jq -r '.[].Event.System.EventID' events.json | sort -n | uniq -c > events.txt
cat events.txt
jq -r '.[] | select(.Event.System.EventID==4769) | .Event.EventData.TargetUserName' events.json | sort | uniq -c | sort -nr
jq -r '.[] | select(.Event.System.EventID==4769) | [.Event.EventData.TargetUserName,.Event.EventData.ServiceName,.Event.EventData.ServiceSid] | @tsv' events.json | sort | uniq -c | sort -nr
jq -r '.[] | select(.Event.System.EventID==4769) | select(.Event.EventData.ServiceName=="MSSQLService")' events.json
jq -r '.[].Event.System.EventID' powershellop.json | sort -n | uniq -c
jq -c '.[] | select(.Event.System.EventID==4104)' powershellop.json | head -2 | tail -1 | jq '.Event.EventData'
jq -c '.[] | select(.Event.System.EventID==4104) | .Event.EventData.Path' powershellop.json | uniq -c
jq -c '.[] | select(.Event.System.EventID==4104) | select(.Event.EventData.Path=="C:\\Users\\alonzo.spire\\Downloads\\powerview.ps1")' powershellop.json | head -1 | jq .Event.System.TimeCreated_attributes.SystemTime
ls C/Windows/prefetch/ | wc -l
ls C/Windows/prefetch/ | grep RUBEUS
PECmd.exe -f ..\campfire-1\Triage\Workstation\2024-05-21T033012_triage_asset\C\Windows\prefetch\RUBEUS.EXE-5873E24B.pf
Timeline
Putting all findings together, this is the confirmed sequence:
powerview.ps1 executed (AD reconnaissance stage).Rubeus.exe executed from C:\Users\Alonzo.spire\Downloads\Rubeus.exe.MSSQLService from 172.17.79.129.Final Answers (for submission)
2024-05-21 03:18:09MSSQLService172.17.79.129powerview.ps12024-05-21 03:16:32C:\Users\Alonzo.spire\Downloads\Rubeus.exe2024-05-21 03:18:08
Artifact and Tool Significance
Artifact significance
SECURITY-DC.evtx:- Best source to confirm Kerberoasting because TGS requests are logged on the DC as
4769. - Provides exact
UTCtime, target service (SPN), requesting account, and source IP. - In this case it answered Q1, Q2, and Q3.
- Best source to confirm Kerberoasting because TGS requests are logged on the DC as
PowerShell-Operational.evtx:- Captures script-block execution (
4104) so tooling and script usage can be verified. - Lets us identify recon scripts by file path and execution time.
- In this case it proved
powerview.ps1and answered Q4 and Q5.
- Captures script-block execution (
Prefetch (RUBEUS.EXE-*.pf):- Endpoint execution evidence independent of event-log parsing.
- Stores executable name, referenced path, run count, and last-run timestamp.
- In this case it confirmed
Rubeus.exepath and time for Q6 and Q7.
Tool significance
Chainsaw:- Fast EVTX triage with Sigma detections and JSON export for deeper analysis.
- Used first to quickly scope suspicious activity.
jq:- Reliable JSON filtering for repeatable forensic extraction.
- Used to isolate
4769/4104and extract answer-grade fields.
PowerView(observed attacker tool):- PowerShell AD reconnaissance toolkit (users, groups, hosts, rights, kerberoastable targets).
- Indicates discovery activity before credential-access actions.
Rubeus(observed attacker tool):- Kerberos abuse toolkit (ticket requests/extraction/manipulation, Kerberoast workflows).
- Indicates ticket abuse and credential-access activity.
PECmd:- Prefetch parser used to decode
.pfartifacts into readable execution details. - Provided executable path and exact run time for Rubeus.
- Prefetch parser used to decode
Reference
- https://0xdf.gitlab.io/2024/06/24/htb-sherlock-campfire-1.html